Every year, the flare-on offers reverse engineering enthusiasts a unique set of puzzles that push our skills and creativity to new limits. This year it was no different. I’ll be writing down a short blog about my experience tackling this years challenges.
Timeline
| Challenge | Date | Time |
|---|---|---|
| Starting of Flare-on | Sep 27 | 6:30 AM |
| frog | Sep 27 | 5:09:55 PM |
| checksum | Oct 1 | 4:46:42 AM |
| aray | Nov 1 | 9:23:14 AM |
| Meme Maker 3000 | Nov 6 | 6:07:38 AM |
| Ending of Flare-on | Nov 8 | 8:00 PM |
Challenge 1 - frog
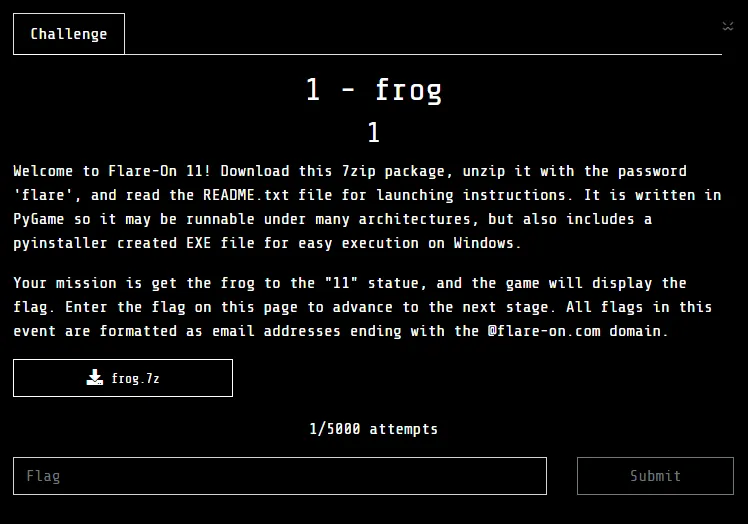
I started my journey with a light warm-up a Python game built using Pygame.
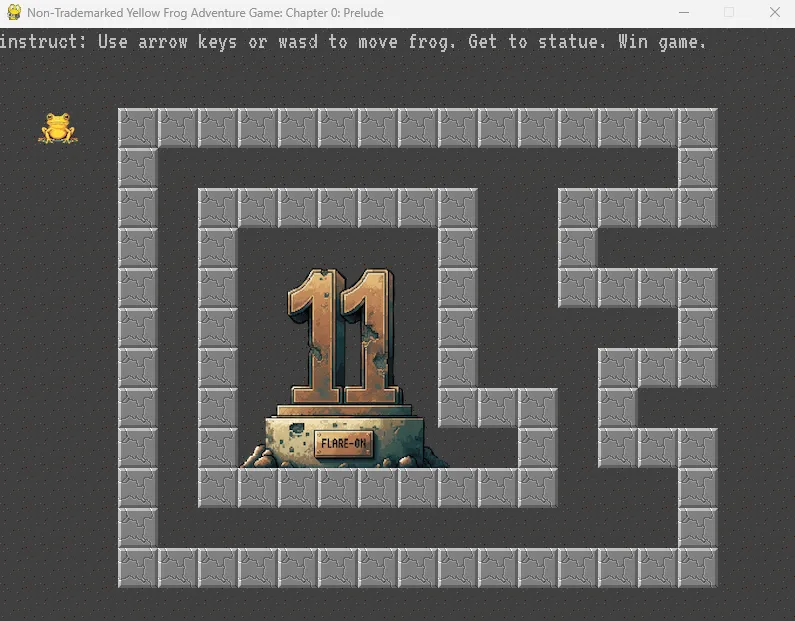
The moment I saw the code, the mechanics clicked. The game’s logic was simple, the encryption straightforward, and within no time, I had my first flag. It was the perfect confidence booster to kick off the competition.
Challenge 2 - checksum
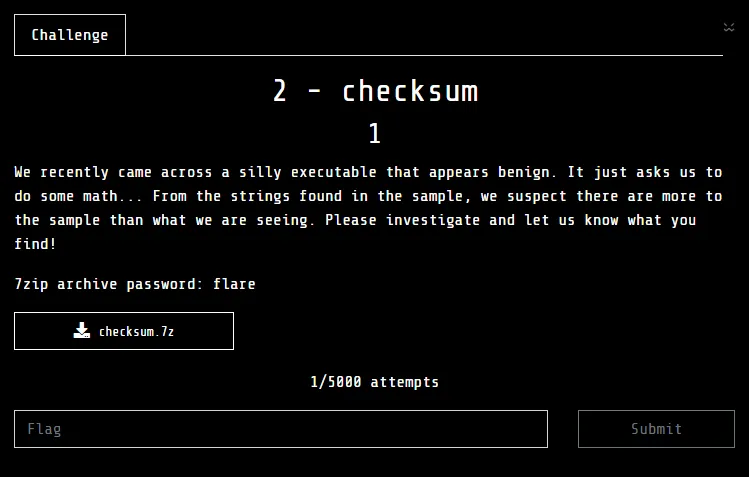
Next came the real test: an executable written in Go. This one demanded every bit of focus I had.
The first battle was against the checksum validation. I had to figure out exactly how the hashing worked, step by step. Once I broke that, a second puzzle appeared finding the exact path where the program was generating the flag image.
Both tasks took time, and at moments, it felt like running in circles. But when I finally pieced it all together, the satisfaction made the struggle worth it.
Challenge 3 - aray
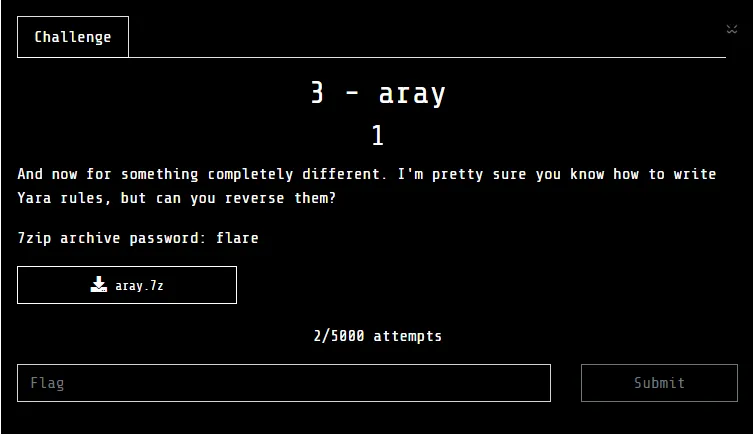
This challenge was a slow burn. The task: work within YARA rule constraints to pass all the conditions. It wasn’t about one clever trick it was about patience and automation.
I began writing a script to systematically test possibilities, and that script grew…and grew…until it reached 407 lines. Every addition brought me one step closer until, finally, the challenge gave in.
Challenge 4 - Meme Maker 3000

The last challenge I cracked was a JavaScript obfuscation puzzle.
The code was messy at first glance, but after some careful deobfuscation and cleanup, the structure became clear. With the browser console as my playground, I poked at it until I understood the exact logic and conditions. Meeting those conditions got me the flag and a big grin.
Wrapping Up
Four challenges out of ten may not sound like much, but for me, it’s a step forward from last year. The progress matters more than the scoreboard.
I walked away with new skills, deeper reverse engineering knowledge, and a renewed drive to push harder next time. This isn’t the end just a break. Next year, I’ll be back, stronger, sharper, and ready for more flags.
:)